Your teams access business applications, SaaS tools, and customer data from a browser. Your service providers too, from positions that you do not control.
The fundamental question: what is the link between these workstations and your applications? What can a compromised endpoint or a malicious individual do once connected to your IS?
The answer depends on your access architecture.
VPN and ZTNA: two generations, same blind spot
The VPN (Virtual Private Network) was designed for a time when applications lived in your data centers. An encrypted tunnel, wide network access. The collaborator connects, he is “inside”.
The problem: the attacker too. According to the “Orange Security Navigator 2026” report, VPNs account for 55% of initial access to corporate information systems in 2025, whether via a compromised account (35%) or the direct exploitation of the tool (20%). Once connected, the computer has direct network access to the IS. Free lateral movement.
The ZTNA (Zero Trust Network Access) addresses this defect. No more global network access: each user accesses only the authorized application, after identity verification. It is real progress.
But the ZTNA stops at the door of the app. The workstation always has direct access to the target application. An attacker can attack the application, its APIs, exfiltrate data, exploit the application as a hub. The ZTNA controls who accesses. Not what the station can do once connected.
The next step: Use a Secure Enterprise Browsing solution
The market has identified this missing link. Analysts are converging on a new category: solutions for Secure Enterprise Browsing (WEB).
The principle: to master the link between the position and the application. Control what the user can do in their session, regardless of the state of their endpoint.
An SEB solution applies Zero Trust principles directly to the browsing session:
- Ongoing identity and context verification
- Granular control of actions (copy and paste, print, upload, screenshot)
- Protecting applications from compromised endpoints
- Visibility on user activity
Not all SEB solutions are created equal
The SEB category brings together very different approaches. And the difference is structural, not cosmetic.
The key question: What is the link between the workstation and the application?
Browser extensions
Agent-based solutions add a layer of security to the existing browser (Chrome, Edge, Firefox) via an extension.
The computer accesses the application directly. The extension observes and enforces policies on top of that. But the link is direct: the local browser loads the DOM, executes the JavaScript, stores the cookies. A compromised computer has access to everything the browser sees, including application data.
Another limitation: the extension must be installed on each workstation. For your employees on controlled workstations, it is manageable. For a service provider, a freelancer, a partner on their own equipment? You have to convince a third party to install a security component on your computer and therefore integrate this parameter into the contract. Friction, deadlines, and sometimes refusal.
Declarative Zero Trust : we verify the identity, then we let the computer interact directly with the application.
Rugged browsers (Enterprise Browser)
A dedicated browser, hardened and controlled by the company.
The environment is more controlled. But the fundamental link does not change: the computer accesses the application directly. Endpoint malware can still exploit this direct connection.
The operational obstacle is even more pronounced: a complete navigator must be installed on each workstation. For uncontrolled populations (third parties, service providers, freelancers) it is even more impacting than an extension. Imposing a browser on users means imposing change management, training and control.
Declarative Zero Trust : the environment is tough, but the workstation remains the access point to the application.
Browser isolation - The only real protocol break
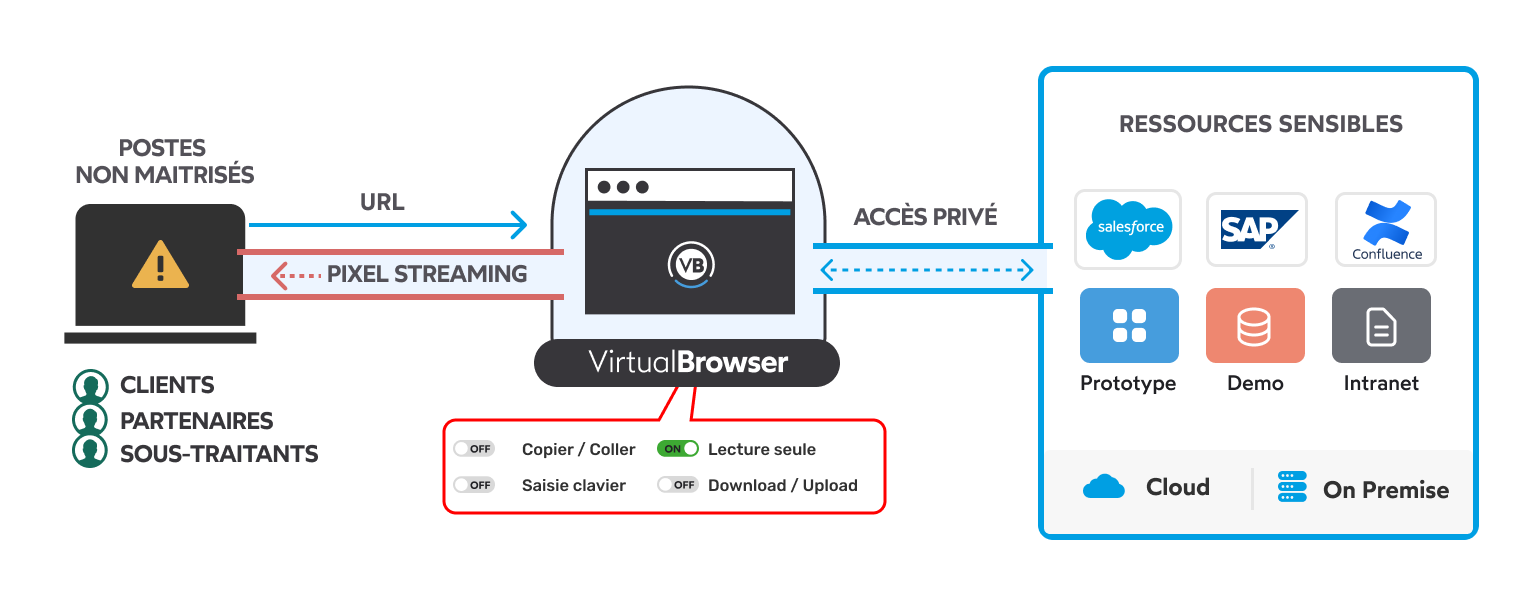
VirtualBrowser breaks the link between the computer and the application. The navigation runs on an isolated server. The station receives a video stream. Nothing else.
SEB solutions protect the browser. VirtualBrowser protects of the navigator.
The computer never touches the application. A compromised workstation or an attacker cannot attack the app or its APIs, or exfiltrate data, or pivot to other areas of the IS. There is no connection to exploit.
On the onboarding side, the contrast is clear. 100% agentless. No extensions to install, no browser to deploy. A service provider, a freelancer, a partner opens a URL from any browser and works immediately. BYOD, unmanaged workstation, unknown equipment, same processing. The application and the IS are protected, regardless of the state of the endpoint.
Structural Zero Trust : the risk is neutralized before reaching the application. By design, not by configuration.
VirtualBrowser: cut the link between uncontrolled workstations and your applications
Concretely, what does it change on a daily basis?
Agentless access. Your users (internal or external) access their applications via a URL. No agents to deploy, no browser to install. A service provider can work in 2 minutes, from any workstation without ever touching your IS directly.
Granular usage control (DLP). Access is not binary. You define what each user can do in their session:
- Read-only consultation, with/without dynamic watermark
- Copy and paste incoming allowed, outgoing blocked
- Upload allowed, download forbidden
- Forbidden prints
Total protocol break. No application data is transmitted to the workstation. The computer cannot attack the application because there is no direct connection to exploit. No DOM to manipulate, no JavaScript to hijack, no cookie to steal. The IS is isolated from the endpoint by design.
What to remember
The security of web access has evolved in three stages: from the network (VPN), to the application (ZTNA), to the session (SEB). At each stage, the link between the position and the resources is tightened.
Within SEBs, the approach counts as much as the category. The discriminating criterion: is the position directly linked to the application? If yes, a compromised endpoint remains a threat to your data and IT - to varying degrees. If not, the risk is neutralized at the source.
VirtualBrowser makes that choice. Physical isolation, pixel streaming, total break between the workstation and the application. An approach validated by certification ANSSI CSPN, which attests to the security level of the solution.


